Privacy-Preserving Data Packet Filtering Protocol with Source IP Authentication | Wireless Personal Communications
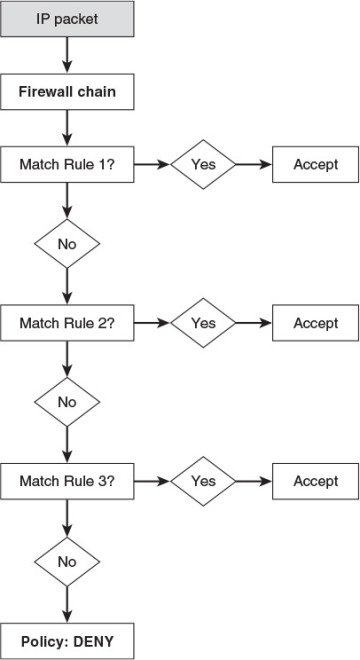
Choosing a Default Packet-Filtering Policy | Packet-Filtering Concepts in Linux Firewalls | InformIT
2.3.2 Firewall and communication basics : JP1/Automatic Job Management System 3 System Design (Configuration) Guide

Filtering Settings Which Use Source IP Addresses (Direct Specification/ Range Specification/ Address Group) : Enterprise Cloud Knowledge CenterEnterprise Cloud 2.0 Tutorial 2.4.0 documentation
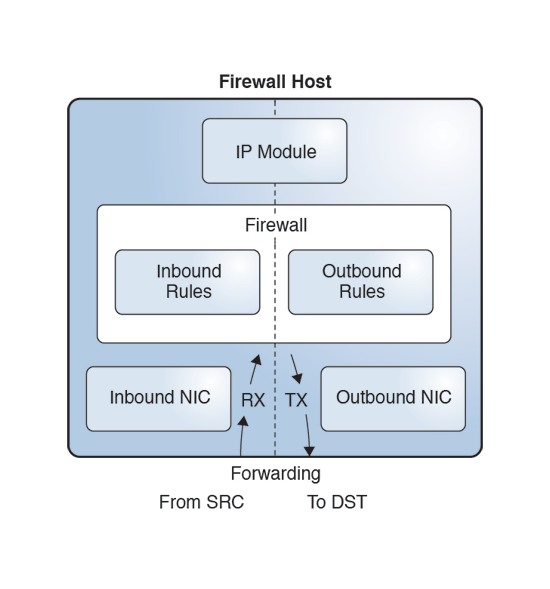

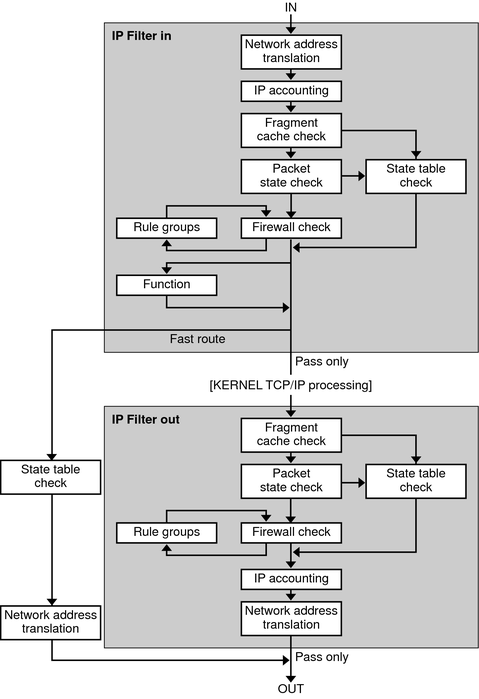







![Chapter 6] Packet Filtering Chapter 6] Packet Filtering](https://litux.nl/Books/Books/www.leothreads.com/e-book/oreillybookself/tcpip/firewall/figs/fire0601.gif)