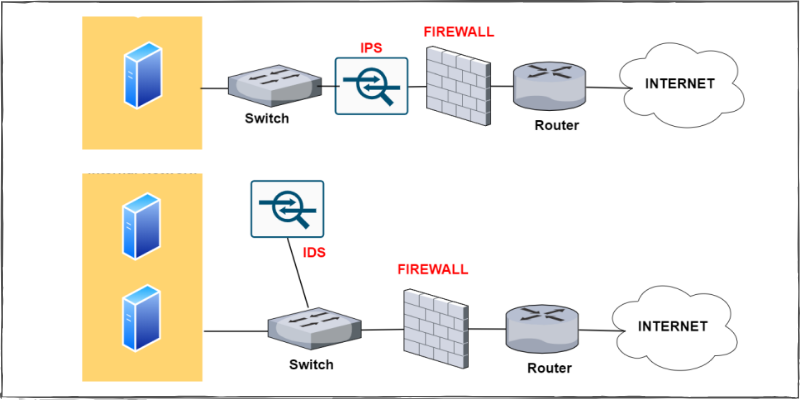
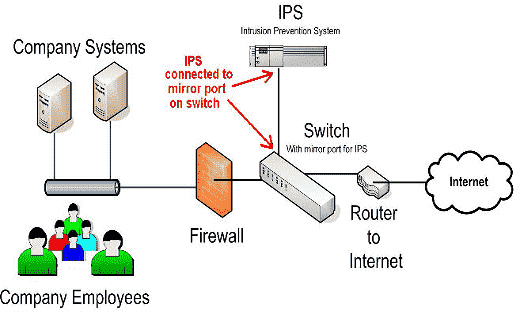
example of a secure network uses IDS/IPS, DMZ, firewall, and proxy.... | Download Scientific Diagram
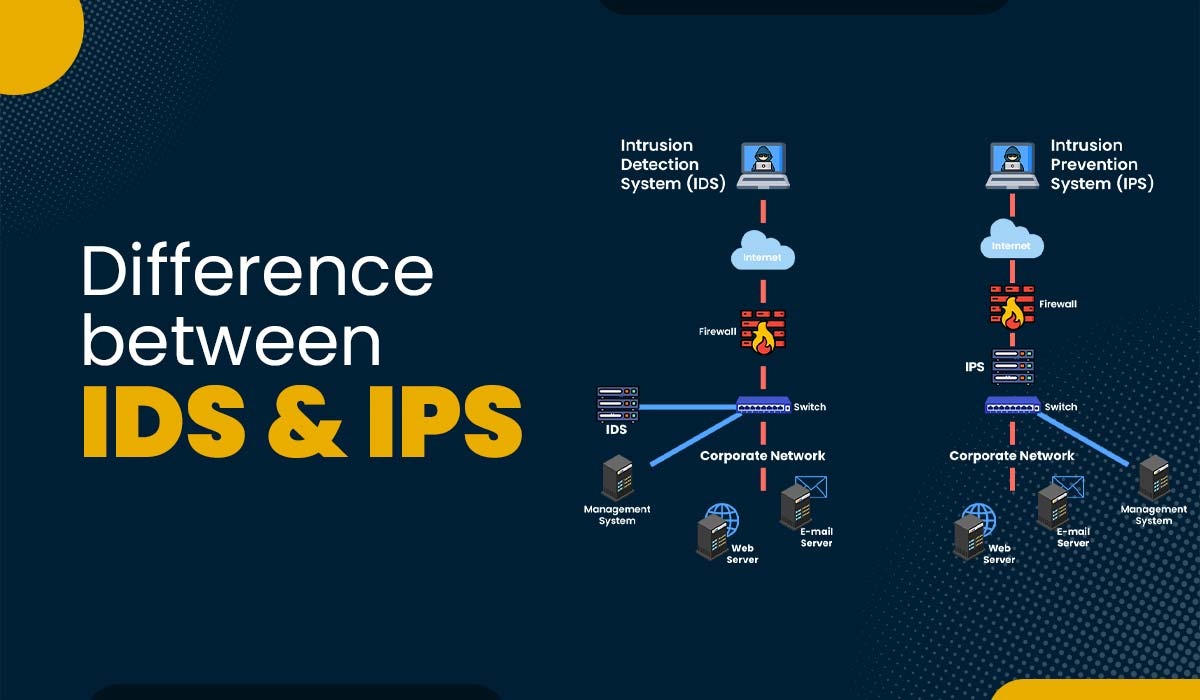
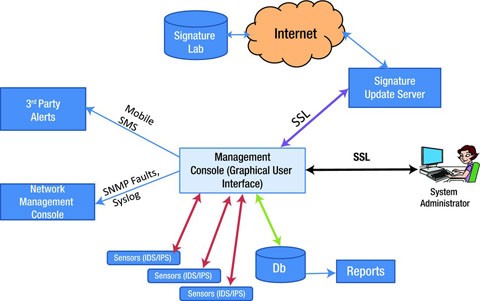
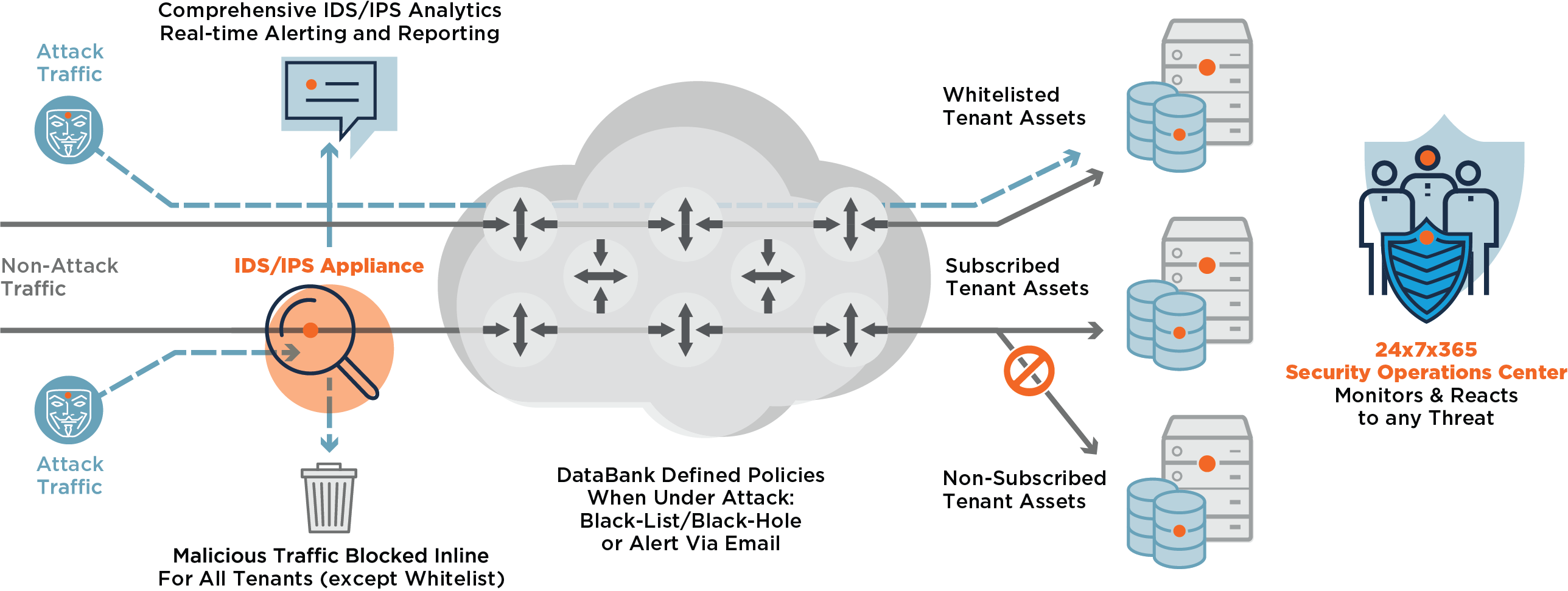
IT Network Intrusion Detection Security | Pune Mumbai Hyderabad Delhi Bangalore India | Valency Networks
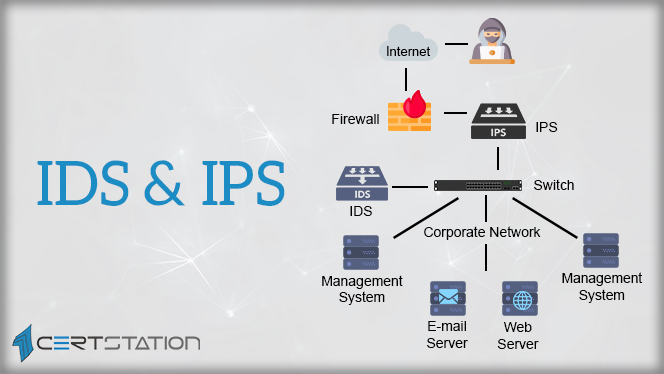
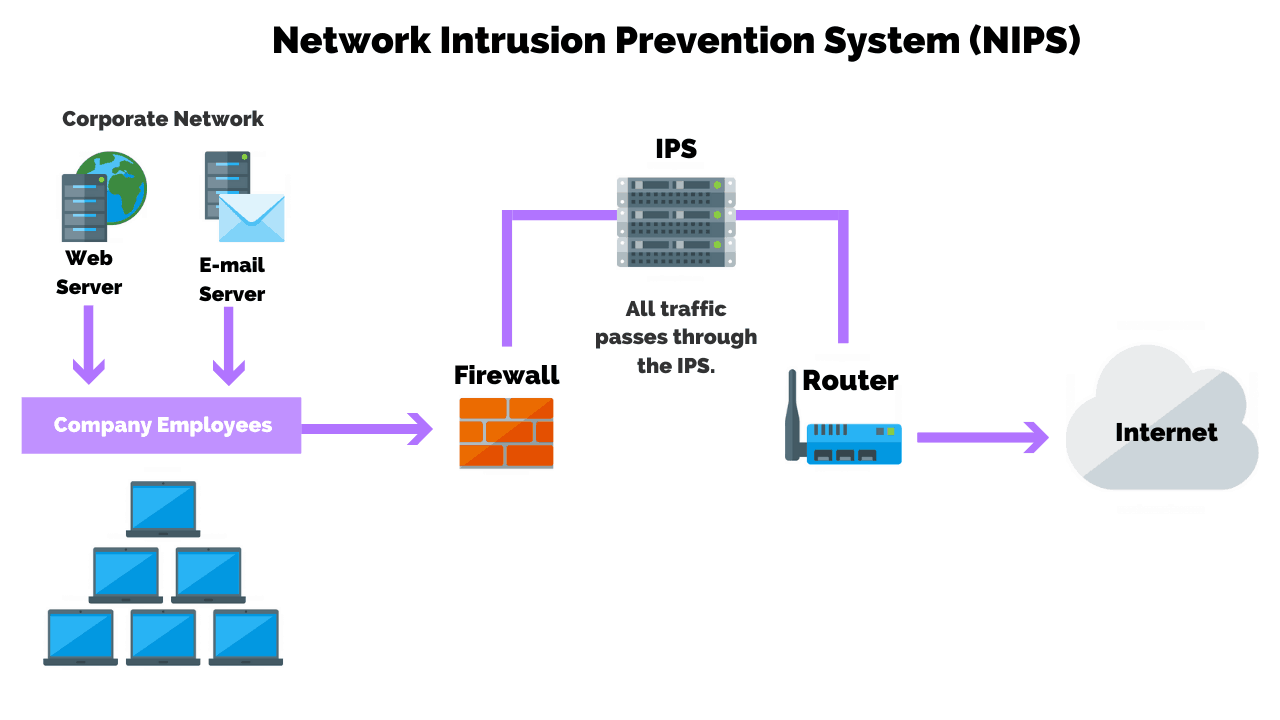
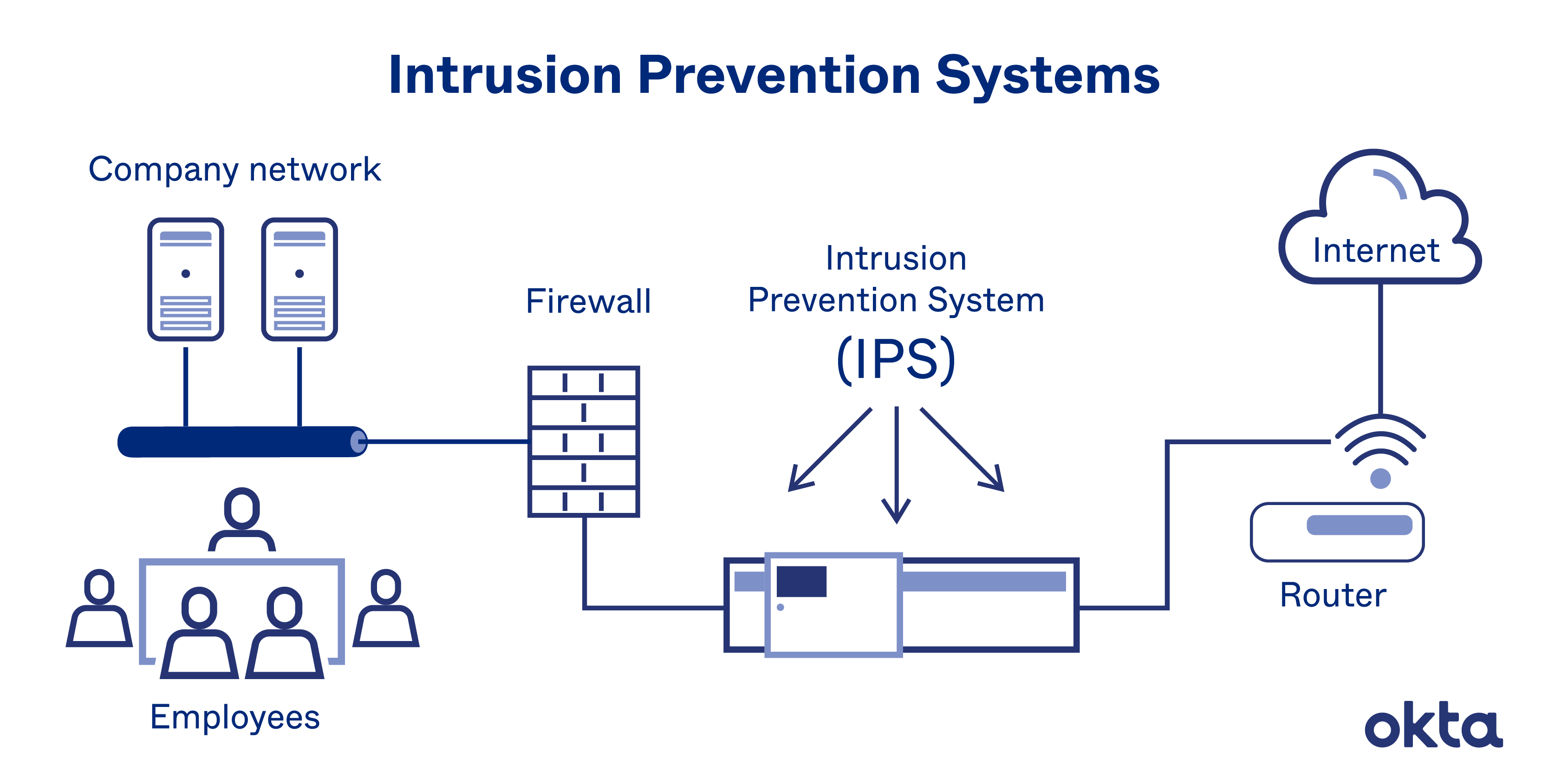
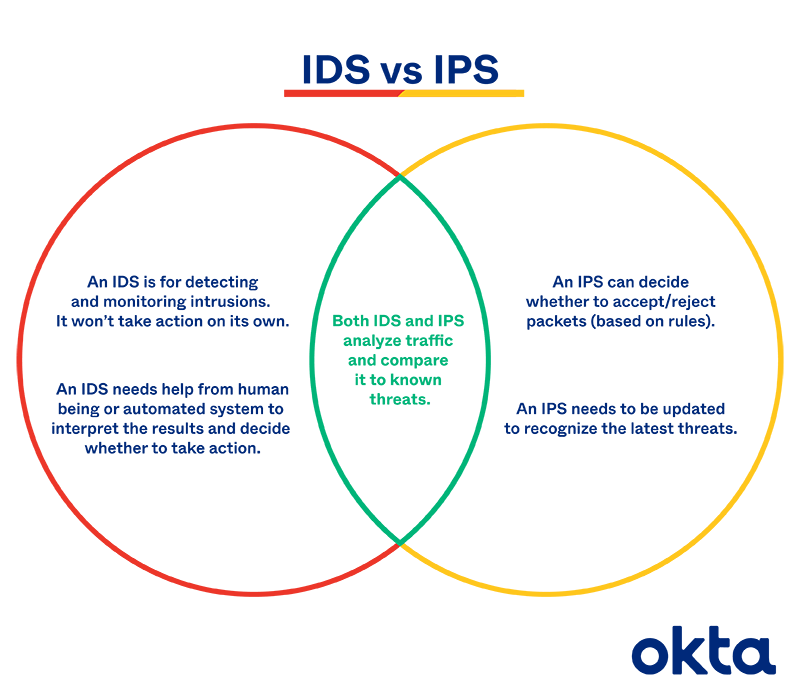
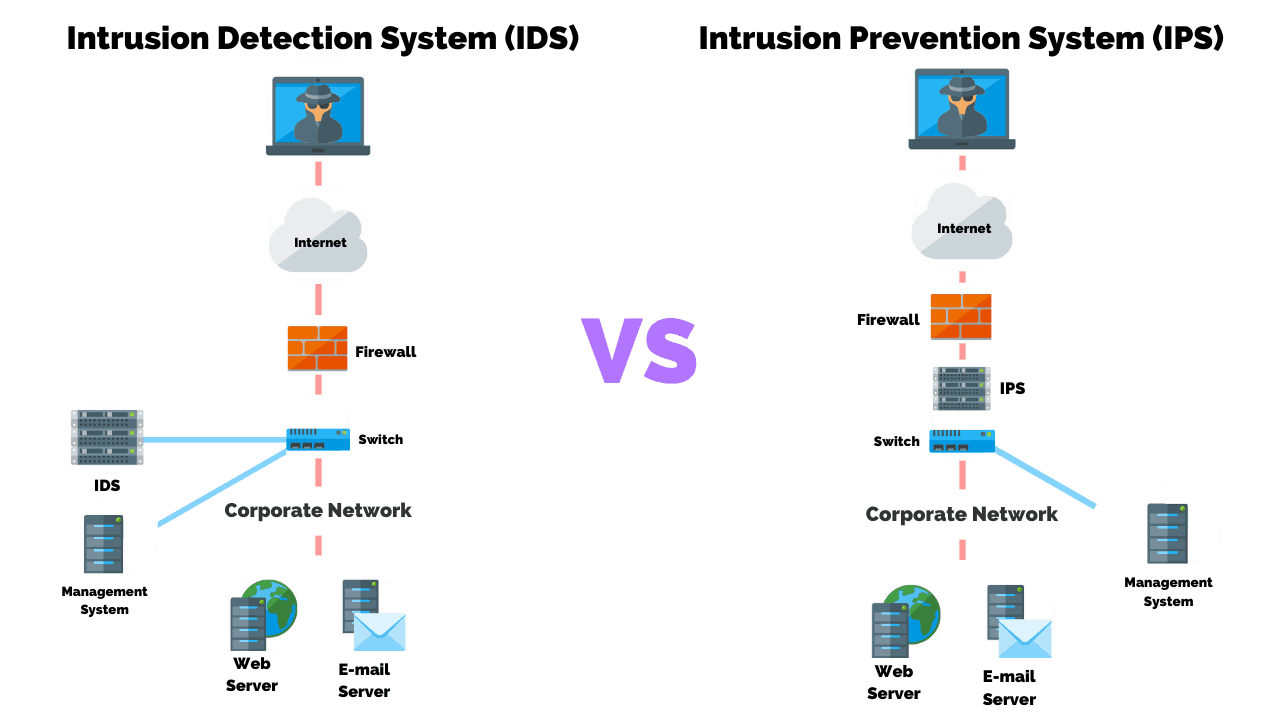
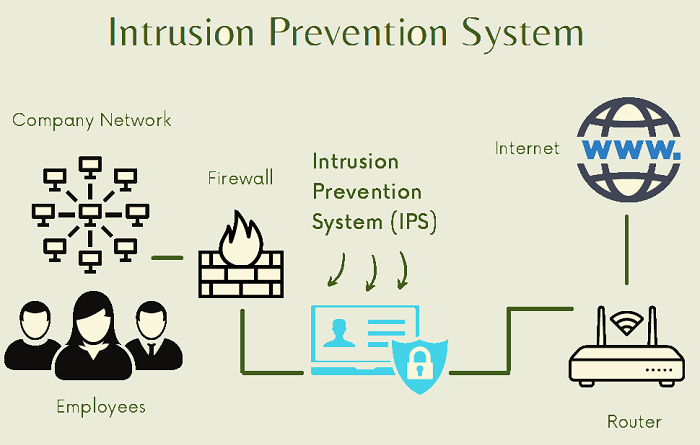
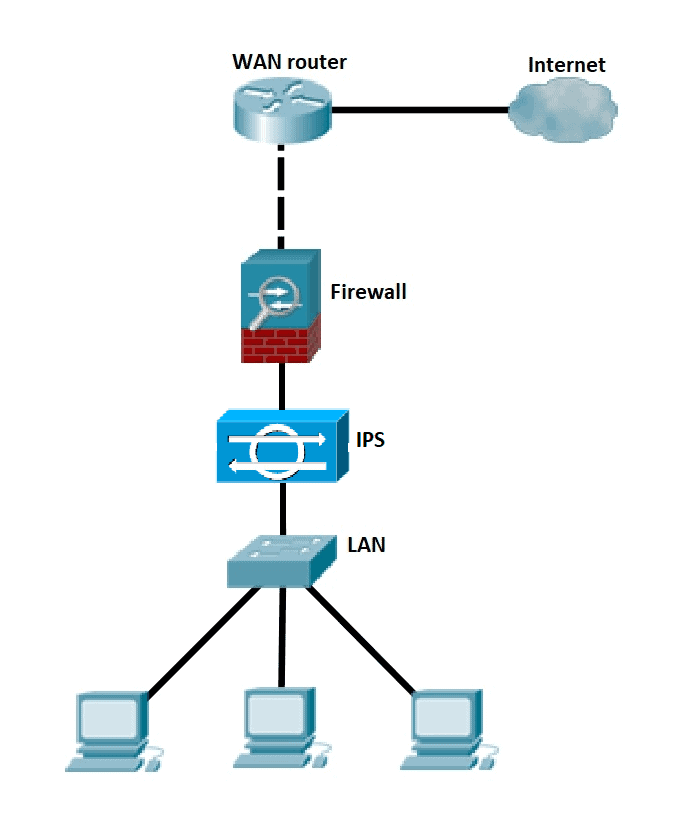
A Detailed Analysis of Intrusion Detection Systems and Intrusion Prevention Systems - CERTStation Blog